December 6, 2022
Faraday in the software development process – GitLab – Part 4
Pentesters use a comprehensive and complete toolkit to…
December 5, 2022
Faraday in the software development process – Jenkins – Part 2
We are going to integrate Jenkins into Faraday with…
November 30, 2022
Faraday in the software development process – Travis – Part 3
Pentesters use a comprehensive and complete toolkit to…
November 29, 2022
Faraday in the software development process – GitHub – Part 1
Pentesters use a comprehensive and complete toolkit to…
November 18, 2022
Exploring the Hidden Attack Surface of OEM IoT devices talk
The security of a company’s network also depends on the…
October 18, 2022
Bypassing passwords and getting a shell through UART in a Wi-Fi router
We started out by trying to connect to the router via UART…
October 5, 2022
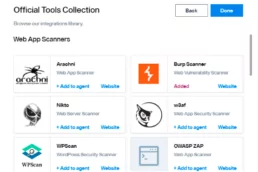
Automating Burp Suite with Faraday
Scaling security testing is hard if you are performing…