Good practices in Cybersecurity – Part 1
Vulnerability ManagementCybersec
February 15, 2024
Pentesters use a comprehensive and complete toolkit to expose different platforms and evaluate the security of an IT infrastructure. They safely try to exploit vulnerabilities and are experts at reporting failures, data leakage, or other vulnerabilities.
In this post, we present these tools and the several ways they can be applied.
SADProtocol goes to Hollywood
January 22, 2024
This research project started when Javier’s wife, our ex Research leader, told him their IP camera had stopped working. Javier was asked to fix it, but, as a security researcher, the temptation was too great. He brought the camera to the office and discussed the problem with Octavio, another security researcher at Faraday. The situation quickly escalated from some light reverse engineering to a full-fledged vulnerability research project, which ended with two high-severity bugs and an exploitation strategy worthy of the big screen.
Release v5.0.0
January 5, 2024
We understand that security is your top priority, and it is our obsession to protect all your digital assets and footprints. However, we recognize that time is equally valuable. It's with pride that we introduce a significant performance enhancement for our users.
Farewell 2023
Vulnerability ManagementCybersec
December 19, 2023
But the outcome of all that is so rewarding. It only placed the bar higher for us, which means we have a tough job for next year. We're saying goodbye to 2023 with a major release. We're pleased to welcome Faraday v.5.0.0. It represents a huge leap in performance for all of our users and customers. We're euphoric about it and very thankful for the team that made it happen. We're a top-tier product that keeps getting better. You can leave your feedback at Gartner and read more about other users' opinions.
First steps in cybersecurity: scan your domain
Red teamPentestingVulnerability Management
December 7, 2023
Pentesters use a comprehensive and complete toolkit to expose different platforms and evaluate the security of an IT infrastructure. They safely try to exploit vulnerabilities and are experts at reporting failures, data leakage, or other vulnerabilities.
In this post, we present these tools and the several ways they can be applied.
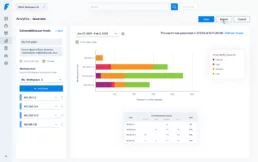
Visualize findings and understand your security posture
PentestingVulnerability Management
November 27, 2023
Our risk scoring system goes beyond mere criticality analysis, pinpointing precisely where real vulnerabilities lie. It offers a straightforward representation, not just an objective evaluation framework, but a curated set of filters tailored to prioritize based on specific contexts. Prioritization becomes a time-saving asset; now, you can filter vulnerabilities from a hacker's perspective.