Our 2022A new year means new opportunities but also new vulnerabilities, and we’re hoping 2023 gives rise to some much-needed progress and safer coverage of your infrastructure. Whatever happens, Faraday will be there, providing security, unique reporting options, and invaluable research work 24/7.
We did this last year.
2022 was an outstanding year for us: our router investigation made it to DefCon, and we developed quite a collection of articles on the security of IoT devices. Plus many write-ups about CTF and reverse engineering. We also released many enhancements in our platform and articles that explain each new feature in depth.
Before starting out on a new cybersecurity journey, here is a quick recap of the most-read notes of 2022.
Most read articles in 2022
Continuous testing, continuous security
A vulnerability in Realtek´s SDK for eCos OS: pwning thousands of routers
Prioritizing: making your Vulnerability Management Manageable
Pentesting toolkit: all you need to know
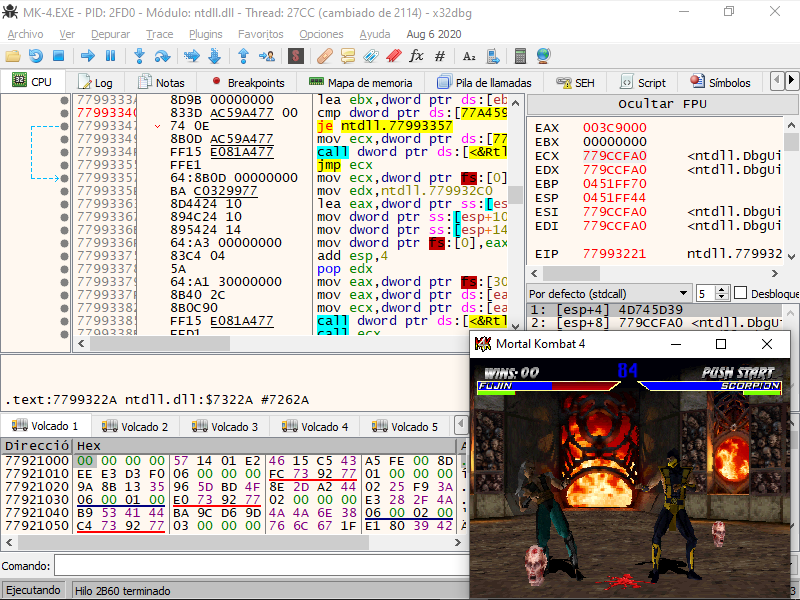
Reverse engineering and game hacking resources
Bypassing password protection and getting a shell through UART in NEC Aterm WR8165N Wi-Fi router