Get a closer look at the platform security teams use to centralize vulnerabilities, prioritize what matters, and move faster from detection to remediation.
We'll start with your contact details to personalize your recommendation
Adjust the values to match your actual security operation
Based on your configuration, here's the plan that best matches your needs.
Scan and enumerate exposed services and open ports (third-party hosts excluded).
Map endpoints, roles and workflows to understand how the application supports business processes.
Map vulnerabilities to specific files and line numbers and provide concrete remediation examples.
Validate server and application security settings, headers, cookie policies, and CSRF defenses.
Combine findings into reproducible Proof-of-Concepts (PoCs) and confirm exploitability in-scope.
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
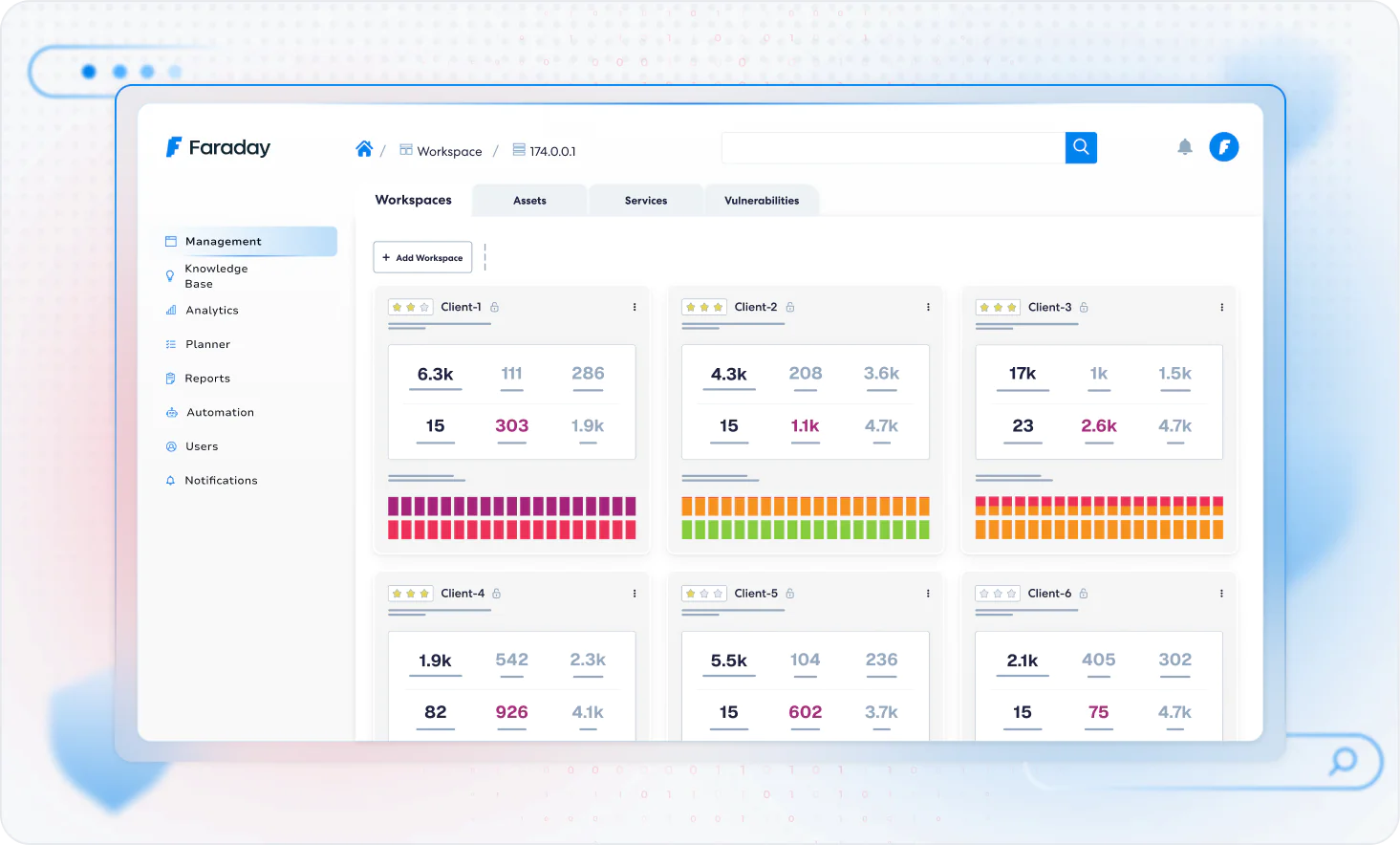
Unlock the full potential of Faraday Platform with our step-by-step tutorials covering key features and functionalities.
Showcase popular tools and platforms compatible with Faraday

Real teams, real results — discover how Faraday transforms workflows worldwide.