Automating Security Tasks
Offensive SecurityRed teamPentestingVulnerability Management
March 16, 2023
In this second part (part one), we will show a step by step of a security analysis having in mind a basic methodology:
- Perform a passive recognition of the target
- Go through an active recognition
- Identify vulnerabilities coming from an automatic scanning
- Exploit these vulnerabilities
- Wrap up with an executive report
2022 Recap: our most read article
Offensive SecurityPentestingVulnerability Management
January 9, 2023
A new year means new opportunities but also new vulnerabilities, and we're hoping 2023 gives rise to some much-needed progress and safer coverage of your infrastructure. Whatever happens, Faraday will be there, providing security, unique reporting options, and invaluable research work 24/7.
Pentesting toolkit: all you need to know
Offensive SecurityRed teamPentesting
November 24, 2022
Pentesters use a comprehensive and complete toolkit to expose different platforms and evaluate the security of an IT infrastructure. They safely try to exploit vulnerabilities and are experts at reporting failures, data leakage, or other vulnerabilities.
In this post, we present these tools and the several ways they can be applied.
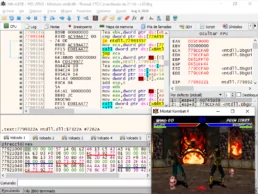
Reverse engineering and game hacking resources
Offensive SecurityRed teamPentestingCybersec
November 9, 2022
If you are curious about reverse engineering, cybersecurity and game hacking, then this is for you too. Happy hacking and keep on learning!
Our CEO Federico Kirschbaum at Argentina Fintech Forum
Offensive SecurityPressCybersec
November 8, 2022
“Security is a culture; you set it up, learn from it, and test it. It is always possible to incorporate security. The sooner, the better, and the easier to scale up.” says Federico Kirschbaum, our CEO at Argentina Fintech Forum
New research findings from Faraday goes to DEF CON
Offensive SecurityRed teamPress
August 11, 2022
Pentesters use a comprehensive and complete toolkit to expose different platforms and evaluate the security of an IT infrastructure. They safely try to exploit vulnerabilities and are experts at reporting failures, data leakage, or other vulnerabilities.
In this post, we present these tools and the several ways they can be applied.