The vulnerability landscape is reaching a breaking point.
In 2025, NIST enriched nearly 42,000 CVEs – 45% more than any prior year. Even so, it was not enough to keep up with the sustained growth in CVE submissions, which have increased significantly since 2020.
Recently, NIST announced a structural change in how the National Vulnerability Database (NVD) operates.
Starting April 2026, the NVD will no longer attempt to fully enrich every CVE. Instead, it will focus on a subset of high-impact vulnerabilities, including:
- CVEs listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog
- Vulnerabilities affecting federal government systems
- CVEs impacting critical software, as defined by Executive Order 14028
Everything else?
Assigned the lowest priority, with no immediate enrichment scheduled — and dependent on manual requests for further analysis.
What this actually means
This is more than an operational adjustment.
It’s a clear signal that the traditional model of vulnerability management, based on full coverage and centralized enrichment — is no longer sustainable.
For security teams, this introduces a new reality:
- Not all vulnerabilities will come with context
- Not all findings will include CVSS, CPE, or CWE data
- And prioritization becomes an internal responsibility
The problem is no longer finding vulnerabilities.
The problem is understanding which ones actually matter.
From detection to prioritization
For years, the industry has focused on detection: more scans, more tools, more findings.
But as volume grows, detection alone stops being useful.
Security teams are now facing a different challenge:
- How to filter signal from noise
- How to correlate findings across sources
- How to prioritize based on real impact
This is where the shift happens:
- From coverage to prioritization
- From volume to impact
- From data to decisions
Where Faraday fits in
This shift aligns directly with the problem we’ve been working on.
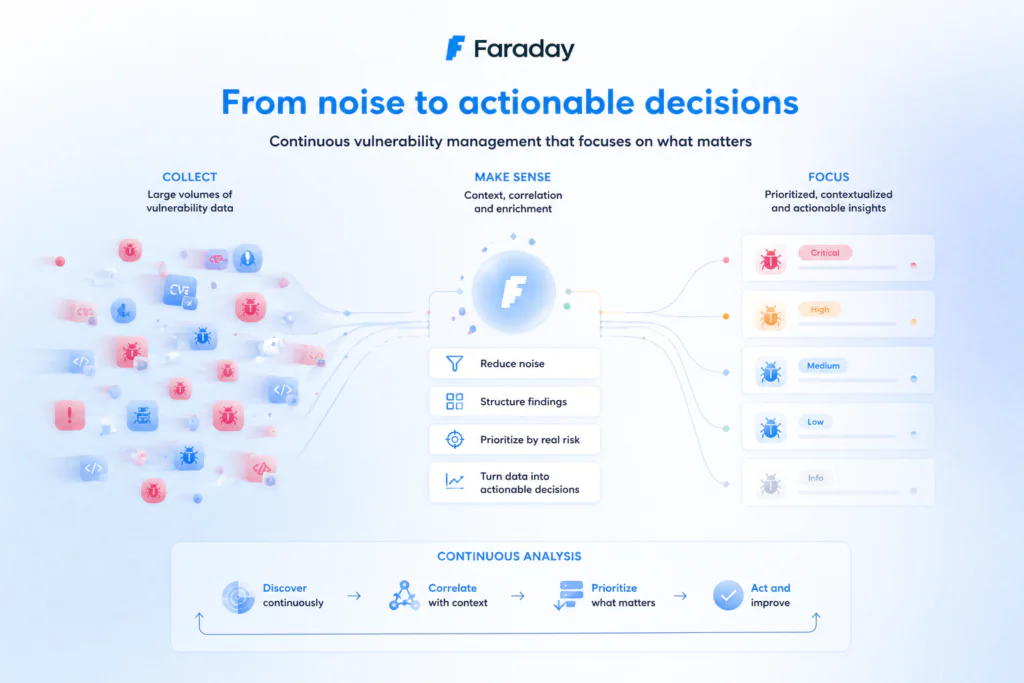
At Faraday, the focus has never been just on collecting vulnerabilities, but on helping teams:
- Reduce noise
- Structure large volumes of findings
- Prioritize based on real risk
- Turn data into actionable decisions
In a world where not all vulnerabilities will be enriched, context, correlation, and prioritization become critical capabilities.
And that’s where platforms built for continuous analysis, not just point-in-time detection, start to make a difference.
The bigger picture
NIST’s decision doesn’t create the problem.
It exposes it.
The volume of vulnerabilities will continue to grow.
Centralized systems will continue to struggle.
And security teams will need to adapt.
Not by finding more vulnerabilities but by getting better at understanding them
Final thoughts
When even the NVD can’t keep up, it’s clear that the industry needs to rethink how vulnerability management works.
The future is not about processing everything.
It’s about focusing on what matters.
If you want to read more about the change:
https://www.nist.gov/news-events/news/2026/04/nist-updates-nvd-operations-address-record-cve-growth