Prioritizing: making your Vulnerability Management Manageable
PentestingVulnerability ManagementCybersec
December 19, 2022
We orchestrate many scanners results at Faraday into the same pipeline. This is how the process starts, but then we devote some time to deciding the importance or urgency of a vulnerability for our company. Cyber Risk
Exploring the Hidden Attack Surface of OEM IoT devices talk
PressPentestingVulnerability ManagementCybersec
November 18, 2022
The security of a company’s network also depends on the security of the home network of its employees. However, most consumer internet-connected devices have a reputation for being vulnerable. This was the starting point for our research team to seek and report security vulnerabilities in IoT devices,
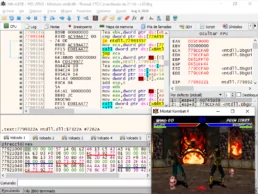
Reverse engineering and game hacking resources
Offensive SecurityRed teamPentestingCybersec
November 9, 2022
If you are curious about reverse engineering, cybersecurity and game hacking, then this is for you too. Happy hacking and keep on learning!
Our CEO Federico Kirschbaum at Argentina Fintech Forum
Offensive SecurityPressCybersec
November 8, 2022
“Security is a culture; you set it up, learn from it, and test it. It is always possible to incorporate security. The sooner, the better, and the easier to scale up.” says Federico Kirschbaum, our CEO at Argentina Fintech Forum
Our team’s vulnerabilities disclosures 2022
Open SourcePentestingVulnerability ManagementCybersec
September 26, 2022
We devote time to reporting vulnerabilities in open-source projects we use every day, but our interests are also linked with IoT, pervasive products that are part of our life. So far, so long, these are the CVEs we reported this year.
Cybersecurity is a secondary objective
Offensive SecurityVulnerability ManagementCybersec
August 1, 2022
A rapidly growing business must choose where to locate its budget. They may continue developing their best product, perform a stronger marketing campaign to continue growing, or reduce the probability of data breaches