Faraday in the software development process – GitHub – Part 1
PentestingVulnerability ManagementWhitepaper
November 29, 2022
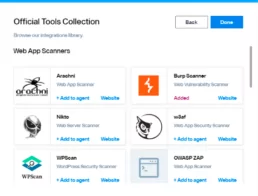
Pentesters use a comprehensive and complete toolkit to expose different platforms and evaluate the security of an IT infrastructure. They safely try to exploit vulnerabilities and are experts at reporting failures, data leakage, or other vulnerabilities.
In this post, we present these tools and the several ways they can be applied.
Exploring the Hidden Attack Surface of OEM IoT devices talk
PressPentestingVulnerability ManagementCybersec
November 18, 2022
The security of a company’s network also depends on the security of the home network of its employees. However, most consumer internet-connected devices have a reputation for being vulnerable. This was the starting point for our research team to seek and report security vulnerabilities in IoT devices,
Release v4.2.0
Vulnerability ManagementLatest Release
November 1, 2022
Optimizing your security posture by drastically reducing the time spent on executing, managing, and prioritizing.
On the security of IoT devices
Open SourcePentestingVulnerability Management
October 24, 2022
According to Cisco’s Annual Internet Report, nearly two-thirds of the global population will have Internet access by 2023. The number of devices connected to IP networks will be more than three times the number of people in the world. Read more about cybersecurity
Bypassing passwords and getting a shell through UART in a Wi-Fi router
Open SourcePressPentestingVulnerability Management
October 18, 2022
We started out by trying to connect to the router via UART and found out that it asks for a username and password in order to log in. We made many attempts using well-known credentials, but we decided that it was time to resort to static analysis in an attempt to find out the correct password.
Automating Burp Suite with Faraday
Open SourcePentestingVulnerability Management
October 5, 2022
Scaling security testing is hard if you are performing manual audits and can create bottlenecks in the development lifecycle. At Faraday, we are always thinking about how to re-use and automate classic workflows; for example, in application security, great tools like Burp Suite Pro provide a great scanner that could provide a security baseline.