We want to make your job easier
Gisela Giusti, our esteemed Product Owner, passionately discusses the significant values behind our tool, while also shedding light on the intricacies that greatly facilitate the work of hundreds of security teams.
Gisela brings an impressive 17-year track record in the cybersecurity industry, having worked with renowned companies like Intel and McAfee. Since joining our team as Product Owner in 2021, she has been vital for the success of our tool, aligning it with our strategic vision and upholding the highest quality standards.
Here is a sneak peak to his work with our platform. What are users of vulnerability management software looking for today? From the area, how do you think about functionality, aesthetics and effectiveness on the same level?
What are users of vulnerability management software looking for today? From the area, how do you think about functionality, aesthetics and effectiveness on the same level?
Vuln management users seek to have a general, orderly and clear vision of the health in their security systems in order to assess and mitigate vulnerabilities.
They look for a platform that helps them identify and catalog vulnerabilities, identify what is urgent and important from what is not, classify them according to their severity and rapidly be able to assess the risk of their systems and networks.
Once the vulnerabilities are identified and classified, users need to take action. Prioritize the steps to follow to mitigate the vulnerabilities (apply patches, correct configurations and anything else necessary). Most of the time these actions are tied to compliance requirements or regulations that organizations have to follow.
Ensuring long-term and continuous security on their systems is also very important for our users. The analysis of data, reports and notifications are of great help to maintain security at an acceptable level for organizations.
From the product and UX area, the functionality is thought from the end user, using feedback from different user profiles. We designed our UI in a way that is friendly for nonsecurity experts but also useful for those who need advanced or specific options to carry out their tasks.
Whenever the functionality allows it, we make the tool more flexible so that it adapts to the needs of each user. For example, we allow the user to format the output of a report with their own logo or even to restructure its content using their own template.
Latest enhancements
On a personal level, what does it feel like or what challenges does working with this type of user that is Faraday’s bring you?
One of the biggest challenges is to listen and address the specific needs of our clients and also ensure that we maintain a comprehensive solution that benefits a variety of users.
Another important challenge is to maintain an adequate level of functionality coverage to meet market expectations and outperform the competition.
What are the improvements that have been introduced to the product in recent months?
Among the most relevant are the following:
– Vulnerability enrichment or Risk score for priorization: Get all the context you need to reduce hundreds of critical vuln into a few. Using internal context information and resorting to external and known data such as CVE, CVSS, trending topic, available exploit, available patch and other indicators vulnerabilities are enriched and all this extra data is used to infer its level of risk.
– New Dashboard Indicators: Using vulnerability enrichment, new, easy-to-understand indicators have been added to help users stay aware of critical issues and take quick action to address them.
– New templates for executive reports: PCI, Web apps
– CVSS v3 Calculator
– Possibility of cataloging the workspaces according to their importance.
– Tools for massive manipulation of vulnerabilities
– New plugins: Invicti, Nessus-SC, Grype, Semgrep, Acunetix 360
– Tags for assets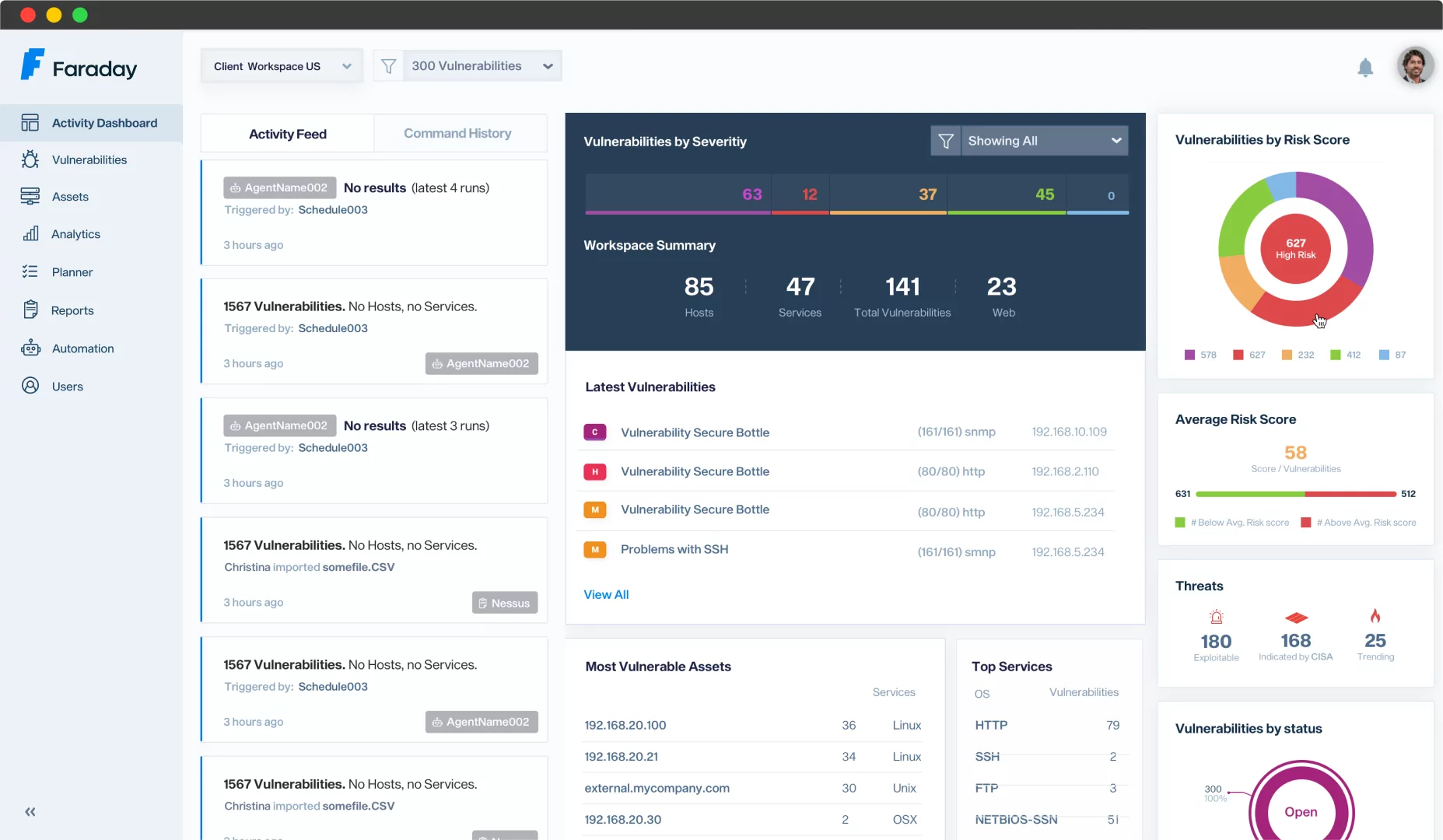 We’d love to hear more about the future of the platform. What does it look like for the rest of this year?
We’d love to hear more about the future of the platform. What does it look like for the rest of this year?
Big changes are coming to the UI. We will restructure sections for friendlier navigation. The goal is for the user to be able to find and manipulate vulnerabilities from all their workspaces at the same time and answer questions such as which is the most critical vulnerability at the moment (without needing to be tied to a specific workspace).
We will also incorporate a dark mode version of the UI, highly anticipated by our users.
Regarding great new functionalities, we will have the extension of the current agents to new agents hosted in the cloud. These agents will be owned by Faraday and can be used to detect vulnerabilities in systems without the need to configure them locally. In the style of the well-known First Scan, the user will be able to choose other agents to scan their networks and obtain the results after a few clicks.
We are also working on a new and extended notification system within the platform but also the email or Slack. The user will be able to configure alerts that are activated when a condition is met and receive notifications of these when they happen. We are planning to keep track of those notifications on a history log to review and manage them over time.
Last but not least, we will offer new reports with weekly/monthly summaries with clear and complete information on the different environments or workspaces. In these reports the user will find information regarding the status of vulnerabilities during the established period, their level of severity and relevant trends compared to previous reports. The top vulnerabilities, the most critical, the most frequent, etc., will be displayed.
What is the future of the tool?
The future of the tool is to accompany users to keep their systems safe and free of vulnerabilities. Organization needs to stay agile and adopt a holistic approach to cybersecurity concerns recognizing that cybersecurity is an ongoing and evolving process, requiring continuous monitoring, adaptation, and improvement.
Continuous and automatic monitoring of your systems using agents in the cloud
Integration with software development processes for early detection of vulnerabilities.
Plus, the use of artificial intelligence for a more sophisticated vulnerability risk analysis.
These enhancements will help security teams tackling the challenge of being one step ahead of an ever growing cyber threat landscape.