Pentesting toolkit: all you need to know

Pentesters use a comprehensive and complete toolkit to expose different platforms and evaluate the security of an IT infrastructure. They safely try to exploit vulnerabilities and are experts at reporting failures, data leakage, or other vulnerabilities.
In this post, we present these tools and the several ways they can be applied.
Wireless
Red Teams focus on auditing security when implementing WIFI networks for a client. For example, they analyze the surroundings of the building with an antenna to check what kind of networks and protections they have. From there, they proceed to implement the right attacks.
Wireless Attack tools:
- Aircrack-ng
- Bettercap
- Kismet
- Reaver
- Wireshark
Cloud
For Cloud coverage, Red Teams will focus on the architecture and services. For example, the way information is stored and how well the lambda function works, as well as data and bucket base implementation.
Cloud Security tools:
- Pacu
- Prowler
- Enumerate-iam
- Scoutsuite
- Cloud-mapper
Web & Infrastructure
The team will assess the external or internal infrastructure in order to identify uncovered ports and services to test them. If they find vulnerabilities, the next phase is to exploit them to prove how exposed the business or application is.
Web Security tool:
- Burp Suite
- Nikto
- Sqlmap
- Gobuster
- Aquatone
Infrastructure Security:
- Nmap
- Brutespray
- Nuclei
- Metasploit
- Nessus
Post-Exploitation tools:
- Bloodhound
- Impacket
- Crackmapexec
Mobile
Static and dynamic security tests will be the center of attention for mobile application pen-testing, iOs, and Android. Red Teams will find failings in implementation by knowing the used framework, how information is stored, and how it communicates with the server.
Mobile Security tools:
- JadX
- mobsf
- apktool
- frida
- logcat
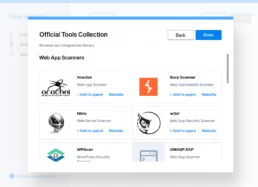
Faraday security platform integrates many of these tools so that any pentester can assess and organize the entire attack surface. This is specially useful when prioritizing and understanding the multiple causes of attack that a company can have.
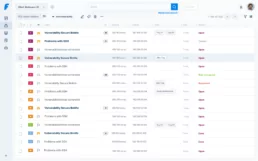
When having a large number of assets scanned with various vulnerabilities, it is very helpful to filter them and know which ones are the most relevant. Moreover, which ones are real and which are false positives.
For any client, having details about every vulnerability found is key. Faraday offers clear and thorough information so that the final report serves as a helpful piece for taking action.
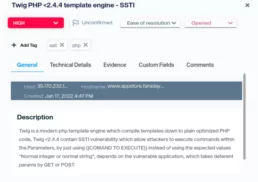
Among the provided information on our dashboards, there are:
- Technical and detailed information about every vulnerability
- References for bigger impact and clarity
- References and indicators on our commitment with guide policies of Confidentiality, Integrity and Availability
Are you interested in our products?👇
Related Posts
September 22, 2025
Lanzamiento Faraday v5.16
¡Bienvenido a la nueva versión de nuestra plataforma de Gestión de Vulnerabilidades! Esta actualización introduce filtros granulares por…
September 22, 2025
Faraday v5.16
Welcome to Faraday v5.16, the new version of our Vulnerability Management platform! This update introduces granular filters by date and…