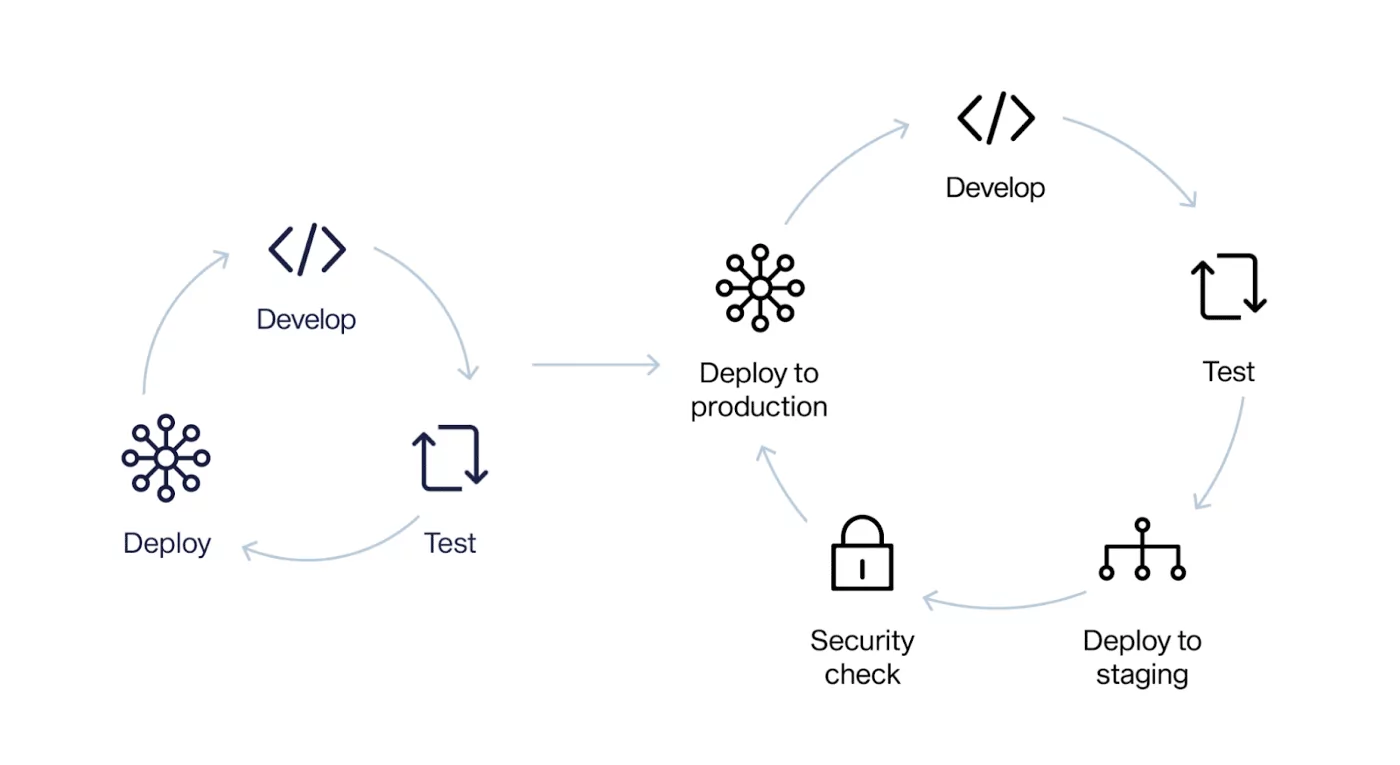
Let’s talk about security into the software development lifecycle. DevSecOps help you identify and mitigate security risks early in the development process, reducing the chance of a breach and improving the overall security of their apps.
This means designing security into the development process from the start. Here are some best practices for implementing DevSecOps in your organization:
1) Shift left: Incorporate security early in the development process by integrating security testing, security-focused code review process and analysis tools into the continuous integration and continuous delivery (CI/CD) pipeline. Security from design to deployment.
 2) Implement automated security testing: Use automated tools to continuously scan the code and infrastructure for vulns, including static application security testing (SAST), dynamic application security testing (DAST), and interactive application security testing (IAST)
2) Implement automated security testing: Use automated tools to continuously scan the code and infrastructure for vulns, including static application security testing (SAST), dynamic application security testing (DAST), and interactive application security testing (IAST)
3)Use secure coding practices: Follow secure coding guidelines, such as OWASP Security guides. They are greatly helpful fOR DevSecOps.
4) Least privilege Principle: Use this approach to limit the access that users and systems have to sensitive resources and data. This reduces the potential damage that can be caused by an attacker or malicious software.
5) Awareness: Train developers and other team members on secure coding practices, and keep them up-to-date on the latest security threats and vulnerabilities. Foster the culture and collaboration between development and security teams. 6) Continuous security and update: Monitor the software in production to identify and address any security issues. Also, keep the software up-to-date with security patches and updates.
6) Continuous security and update: Monitor the software in production to identify and address any security issues. Also, keep the software up-to-date with security patches and updates.